Patrick's Blog
Monday, September 14, 2015
Sunday, July 25, 2010
Computer Ethics Sample Situation
When computers first began to be used in society at large, the absence of ethical standards about their use and related issues caused some problems. However, as their use became widespread in every facet of our lives, discussions in computer ethics resulted in some kind of a consensus. Today, many of these rules have been formulated as laws, either national or international. Computer crimes and computer fraud are now common terms. There are laws against them, and everyone is responsible for knowing what constitutes computer crime and computer fraud.
Here is a situation portraying to computer ethics:
Plagiarism is the taking of the ideas, writings, drawings, words, or other similar intellectual property created by others and presenting it as your own. For example, you can reuse writings in the public domain without worrying about the legal problem of infringing a copyright, but presenting them as your own without proper credit to their true origin is an act of plagiarism. And plagiarism is unethical.
Here is a situation portraying to computer ethics:
Plagiarism is the taking of the ideas, writings, drawings, words, or other similar intellectual property created by others and presenting it as your own. For example, you can reuse writings in the public domain without worrying about the legal problem of infringing a copyright, but presenting them as your own without proper credit to their true origin is an act of plagiarism. And plagiarism is unethical.
Sunday, July 4, 2010
Foundation Day Remarks
The 12th PSHS-CMC Foundation Day, as expected in a previous blog post, is fun and exiting. I was not able to join any game on the two day celebration. I was helping my fellow SCS officers facilitate the games. Anyways, I kept myself happy by eating Cornetto. I am also happy because there were new Green league members. I am looking forward to the 13th PSHS-CMC Foundation Day. Will blog you soon!
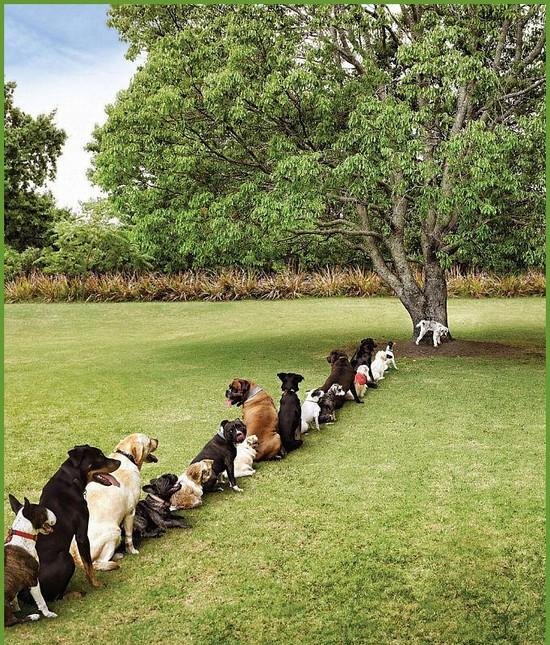
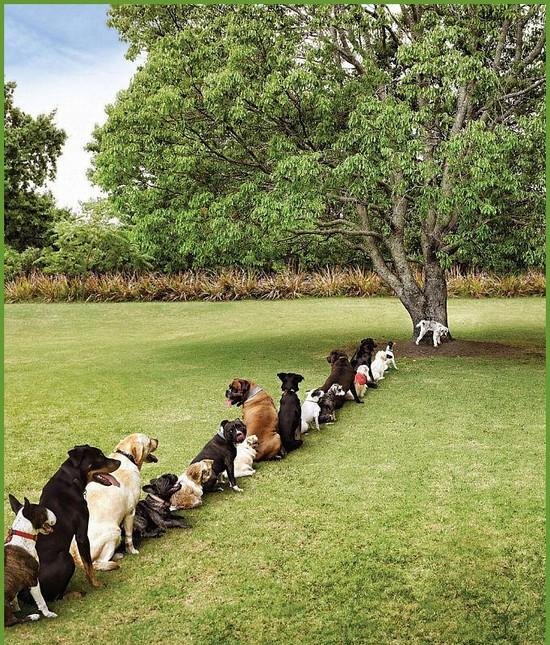
Problem for dogs and by Mr. Claus
I just realized were not not the only ones having problems with deforestion. Dogs have their problems too. How? here's how...
Maybe, just maybe, Santa Claus may be the one who spread the Influenza AH1N1 Flu Virus from children to children while delivering their presents. But this is 99.99% uncertain cause Santa doesn't go out in the middle of April. But there's no harm in making sure it will never happen.

Maybe, just maybe, Santa Claus may be the one who spread the Influenza AH1N1 Flu Virus from children to children while delivering their presents. But this is 99.99% uncertain cause Santa doesn't go out in the middle of April. But there's no harm in making sure it will never happen.

Tuesday, June 29, 2010
Why the wedding ring should be put on the fourth finger?
First, center fingers bended and put together back to back. Second, the rest 4 fingers tips to tips.
Try to open your thumb, the thumb represent our parents. It can be opened because all human does go thru sick and dead; in which our parents will leave us one day.
Now close your thumb and open your second finger. It represents our brothers and sisters, they do have their own family but they too will leave us one day.
Now close your second finger and open up your little finger. It represents our children who sooner or later, they too will leave us for they got their own life to live.
Finally, close your little finger and try to open your fourth finger where we put our wedding ring.You will be surprise to find out that it cannot be opened at all!
Why, because it represents husband and wife, the whole life that you will be attached to each other. Real love that will stick together forever and ever!
Thumb represent parents Second finger represent brothers & sisters Center finger represent own self Fourth finger represent your partner Last finger represent your children.

Try to open your thumb, the thumb represent our parents. It can be opened because all human does go thru sick and dead; in which our parents will leave us one day.
Now close your thumb and open your second finger. It represents our brothers and sisters, they do have their own family but they too will leave us one day.
Now close your second finger and open up your little finger. It represents our children who sooner or later, they too will leave us for they got their own life to live.
Finally, close your little finger and try to open your fourth finger where we put our wedding ring.You will be surprise to find out that it cannot be opened at all!
Why, because it represents husband and wife, the whole life that you will be attached to each other. Real love that will stick together forever and ever!
Thumb represent parents Second finger represent brothers & sisters Center finger represent own self Fourth finger represent your partner Last finger represent your children.

Friday, June 25, 2010
Best Dad! Cake
Before we opened the box, I said "No thanks, it's just another chocolate cake from Red Ribbon." Flip one side down, and another, and another , and another, and finally the top. Wow! Simply unique! chocolate cake surround by sweet icing! Gi picture gyud nako before we ate.
The icing is very very very sweet. Too sweet for me. Thank you to the person (one of my father's patients) who gave this! (not to me, my father). My favorite part: Buttons!
The icing is very very very sweet. Too sweet for me. Thank you to the person (one of my father's patients) who gave this! (not to me, my father). My favorite part: Buttons!
Ten Commandments of Computer Ethics
1. Thou shalt not use a computer to harm other people.
2. Thou shalt not interfere with other people's computer work.
3. Thou shalt not snoop around in other people's files.
4. Thou shalt not use a computer to steal.
5. Thou shalt not use a computer to bear false witness.
6. Thou shalt not use or copy software for which you have not paid.
7. Thou shalt not use other people's computer resources without authorization.
8. Thou shalt not appropriate other people's intellectual output.
9. Thou shalt think about the social consequences of the program you write.
10. Thou shalt use a computer in ways that show consideration and respect.
2. Thou shalt not interfere with other people's computer work.
3. Thou shalt not snoop around in other people's files.
4. Thou shalt not use a computer to steal.
5. Thou shalt not use a computer to bear false witness.
6. Thou shalt not use or copy software for which you have not paid.
7. Thou shalt not use other people's computer resources without authorization.
8. Thou shalt not appropriate other people's intellectual output.
9. Thou shalt think about the social consequences of the program you write.
10. Thou shalt use a computer in ways that show consideration and respect.
Subscribe to:
Posts (Atom)
